Darknet Diaries Episode Details
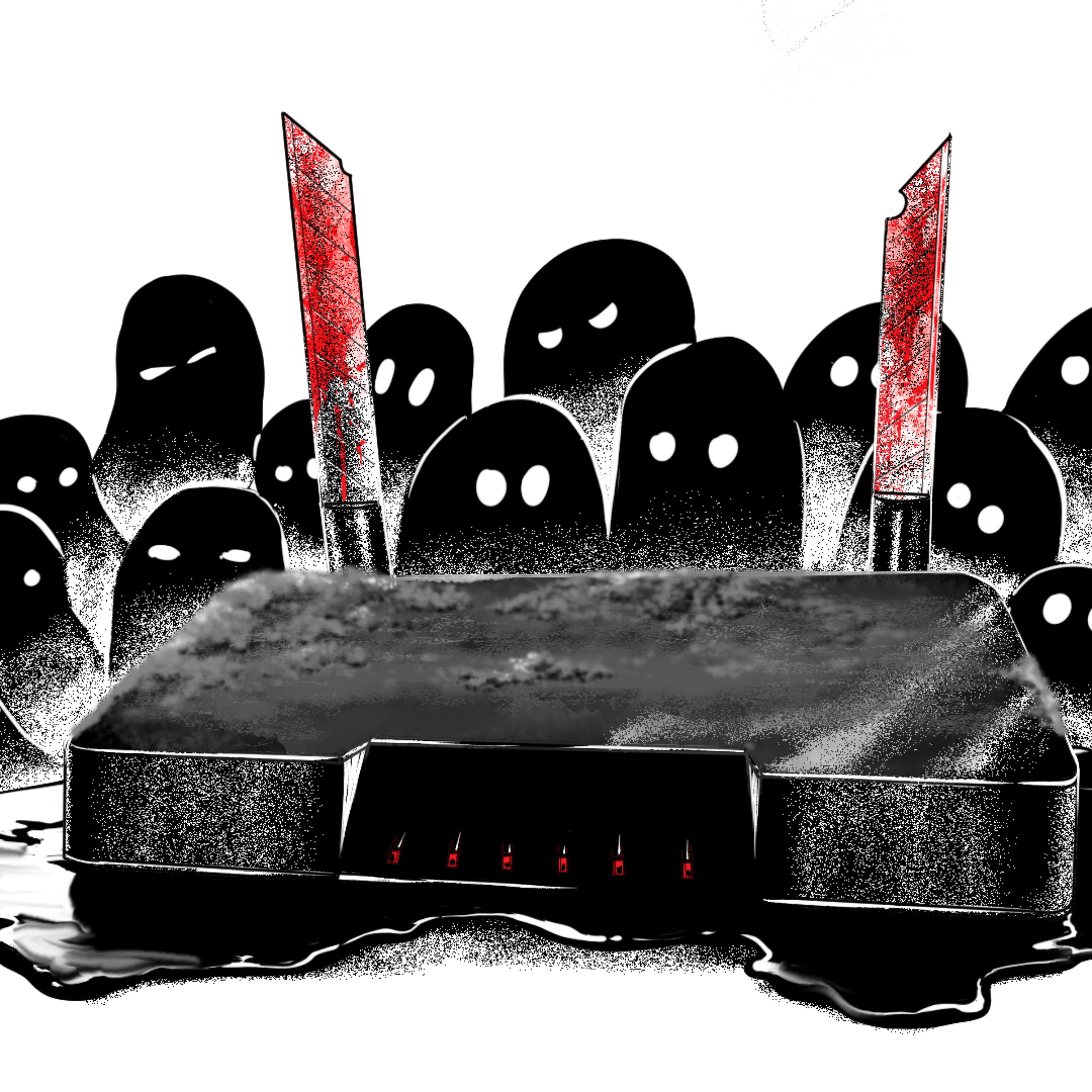
What if there was a device which gave you endless movies and TV shows without ads? Ok great sign me up! In this episode we interview “D3ada55”, who found such a device, but as she gazed into it, she discovered it gazing back at her. Sponsors Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com. This episode is sponsored by Meter, the company building networks from the ground up. Meter delivers a complete networking stack - wired, wireless, and cellular - in one solution that’s built for performance and scale. Alongside their partners, Meter designs the hardware, writes the firmware, builds the software, manages deployments, and runs support. Learn more at meter.com. This episode is sponsored by Exaforce. Exaforce was created to handle the complete security operations workflow - detect, triage, investigate, respond. Exabots autonomously manage every stage, eliminating gaps between alert and action that slow down traditional security operations. And how it works is simple too: the exabots ingest all security data and then semantically connects it to understand the full context of security events and how they relate to each other. Learn more at exaforce.com/darknet-diaries.